- Mark as New
- Bookmark
- Subscribe
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
09-22-2021 10:38 PM (Last edited 09-22-2021 11:21 PM ) in
Tech Talk
Trojans are generally spread by some form of social engineering, for example where a user is duped into executing an email attachment disguised to appear not suspicious, (e.g., a routine form to be filled in), or by clicking on some **bleep** advertisement on social media or anywhere else. Although their payload can be anything, many modern forms act as a backdoor, contacting a controller which can then have unauthorized access to the affected computer.[6] Ransomware attacks are often carried out using a trojan.
Unlike computer viruses, worms, and rogue security software, trojans generally do not attempt to inject themselves into other files or otherwise propagate themselves.
It's not clear where or when the concept, and this term for it, was first used, but by 1971 the first Unix manual assumed its readers knew both
Also, one may not change the owner of a file with the set—user—ID bit on, otherwise one could create Trojan Horses able to misuse other’s files.
Another early reference is in a US Air Force report in 1974 on the analysis of vulnerability in the Multics computer systems.
It was made popular by Ken Thompson in his 1983 Turing Award acceptance lecture "Reflections on Trusting Trust",[10] subtitled: To what extent should one trust a statement that a program is free of Trojan horses? Perhaps it is more important to trust the people who wrote the software. He mentioned that he knew about the possible existence of trojans from a report on the security of Multics.
Once installed, trojans may perform a range of malicious actions. Many tend to contact one or more Command and Control (C2) servers across the Internet and await instruction. Since individual trojans typically use a specific set of ports for this communication, it can be relatively simple to detect them. Moreover, other malware could potentially "take over" the trojan, using it as a proxy for malicious action.
In German-speaking countries, spyware used or made by the government is sometimes called govware. Govware is typically a Trojan software used to intercept communications from the target computer. Some countries like Switzerland and Germany have a legal framework governing the use of such software. Examples of govware trojans include the Swiss MiniPanzer and MegaPanzer[16] and the German "state trojan" nicknamed R2D2. German govware works by exploiting security gaps unknown to the general public and accessing smartphone data before it becomes encrypted via other applications.
Due to the popularity of botnets among hackers and the availability of advertising services that permit authors to violate their users' privacy, trojans are becoming more common. According to a survey conducted by BitDefender from January to June 2009, "trojan-type malware is on the rise, accounting for 83% of the global malware detected in the world." Trojans have a relationship with worms, as they spread with the help given by worms and travel across the internet with them. BitDefender has stated that approximately 15% of computers are members of a botnet, usually recruited by a trojan infection.
Private and governmental
• ANOM - FBI
• 0zapftis / r2d2 StaatsTrojaner – DigiTask
• DarkComet – CIA / NSA
• FinFisher – Lench IT solutions / Gamma International
• DaVinci / Galileo RCS – HackingTeam
• Magic Lantern – FBI
• SUNBURST – SVR/Cozy Bear (suspected)
• TAO QUANTUM/FOXACID – NSA
• WARRIOR PRIDE – GCHQ
Publicly available
• EGABTR – late 1980s
• Netbus – 1998 (published)
• Sub7 by Mobman – 1999 (published)
• Back Orifice – 1998 (published)
• Y3K Remote Administration Tool by E&K Tselentis – 2000 (published)
• Beast – 2002 (published)
• Bifrost trojan – 2004 (published)
• DarkComet – 2008-2012 (published)
• Blackhole exploit kit – 2012 (published)
• Gh0st RAT – 2009 (published)
• MegaPanzer BundesTrojaner – 2009 (published)
• MEMZ by Leurak – 2016 (published)
Detected by security researchers
• Twelve Tricks – 1990
• Clickbot.A – 2006 (discovered)
• Zeus – 2007 (discovered)
• Flashback trojan – 2011 (discovered)
• ZeroAccess – 2011 (discovered)
• Koobface – 2008 (discovered)
• Vundo – 2009 (discovered)
• Meredrop – 2010 (discovered)
• Coreflood – 2010 (discovered)
• Tiny Banker Trojan – 2012 (discovered)
• Shedun Android malware – 2015 (discovered)
The computer term "trojan horse" is derived from the legendary Trojan Horse of the ancient city of Troy. For this reason "Trojan" is often capitalized. However, while style guides and dictionaries differ, many suggest a lower case "trojan" for normal use.

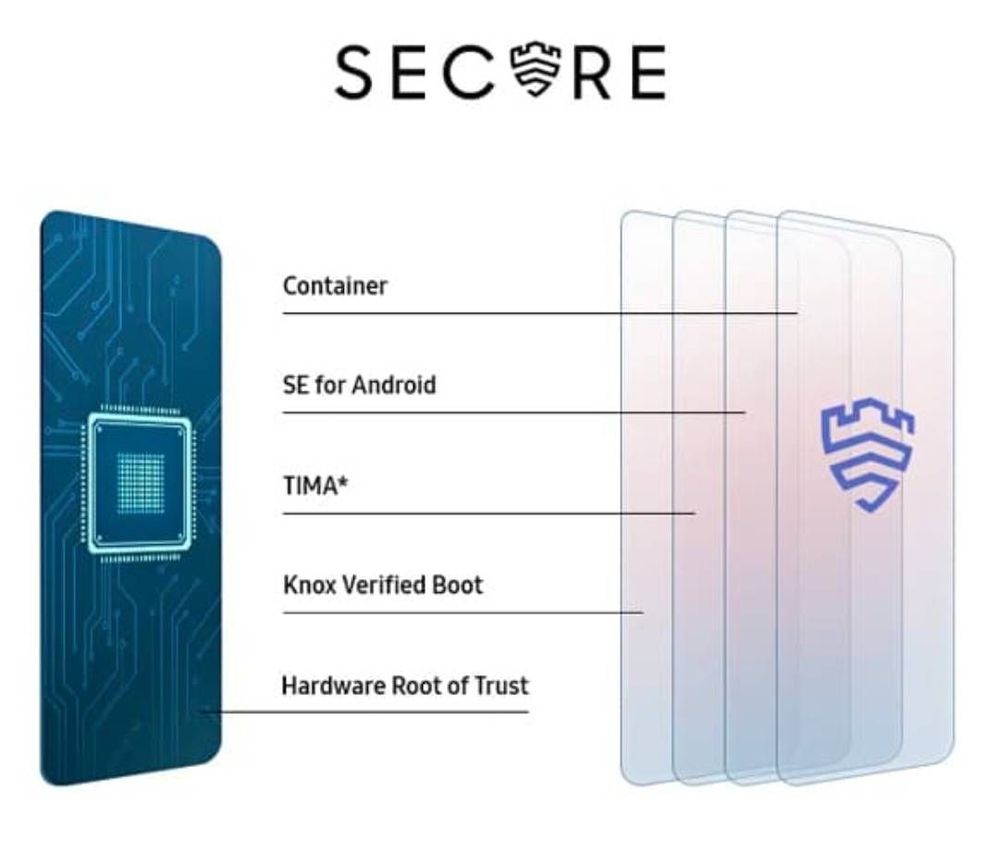
Knox is a multi-layered platform built into both the hardware and software of Samsung’s latest devices. Knox constantly verifies the integrity of the device through a chain of security checks that begin at the platform level and extend to the operating system, and detects any tampering to ensure your data is always secure. This secure system can be used for all users — be it a common daily smartphone user to enterprise-level requirements. Samsung’s Knox platform is built into their smartphones, tablets, and wearables at the manufacturing stage itself.

Why is Knox important?
Samsung’s Knox helps companies ensure that the devices used by employees have isolated personal and business data environments to prevent sensitive company information if the risk of loss or theft.
How does this function?
A simple press on the Samsung Knox icon on a compatible Samsung Android smartphone will automatically switch between personal and business modes, and allows to seamlessly navigate between the encrypted content. No need to reboot the device.
-> Knox is actually beneficial in an enterprise environment where the administrators can use it to keep business and personal data separate and secure, ensuring that no threat is caused by an unknown application or a potential user to the business data. In short, what you do in your personal space on your phone, cannot be sent or pushed to the business layer, and vice versa, to ensure that data is safe and not leaked out. Hence, the isolation on the two layers makes it easier for companies to manage and monitor their data’s safety. Since the employees will surely be using the smartphone at home and on insecure wireless connections around the world, it is necessary that businesses isolate that behavior. In short, employees can use a common device for both their business and personal needs, and Samsung’s Knox is a technology that allows business and personal data to securely coexist on the same handset.
When does Knox work?
Knox will not only work your device when it is switched on, it also protects your device when it boots and also when it is switched off. Even when your device is off, all your data is encrypted by default. The encryption key is stored in a secure area called TrustZone in the device chipset. During boot-up, Knox platform checks for authorized (unrooted) firmware and checks for device software integrity. At run-time, the kernel is continuously monitored and protected. If compromised, security-sensitive apps are locked.
- « Previous
- Next »
- Mark as New
- Subscribe
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-21-2021 09:07 AM in
Tech Talk- Mark as New
- Subscribe
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
12-22-2021 01:26 PM in
Tech Talk- Mark as New
- Subscribe
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-29-2024 04:56 PM in
Tech TalkIf we talk about optimal solutions for cybersecurity, then you can consider cloud storage, as well as corporate e-mail by Beeble https://beeble.com/en/about-project. By connecting an email domain or simply using this cloud storage, you don’t have to worry about scammers, information leaks and other problems that we encounter every day.
- « Previous
- Next »
