- Mark as New
- Bookmark
- Subscribe
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
06-22-2020 05:08 PM in
Tech TalkWhat is Samsung Knox ??
Samsung Knox is a leading mobile security solution that provides a SECURE environment for corporate data and apps for all Galaxy devices. It PROTECTS your business and personal privacy from one device without the need for third party IT protection.
Why it is required ??
The phenomenal growth in use of smartphones and tablets, along with our sometimes not-so-smart attitude to security, means that our mobile devices are easy and plentiful targets. As well as containing masses of valuable personal data, our mobiles are the perfect way for cybercriminals to get at us.
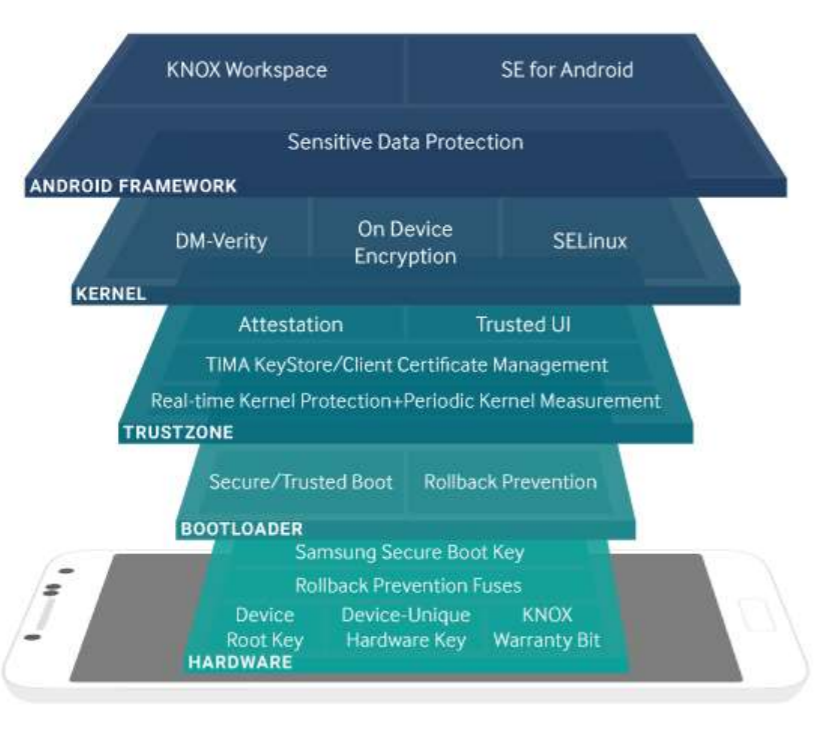
From the minute your smartphone is powered on, you know it will keep your device safe, thanks to a multi-layered approach to security that begins in the factory.
Samsung creates a device root key and a device-unique hardware key at the point of manufacture. These are public/private key pairs, unique to each device that are created and stored in a part of the CPU known as the Trusted Execution Environment (TEE). Access to this zone and the information stored on it is tightly regulated.
These keys form the basis of the rest of the features which Samsung provides through its security platform.
Other Devices Security V/s Samsung Knox Security.
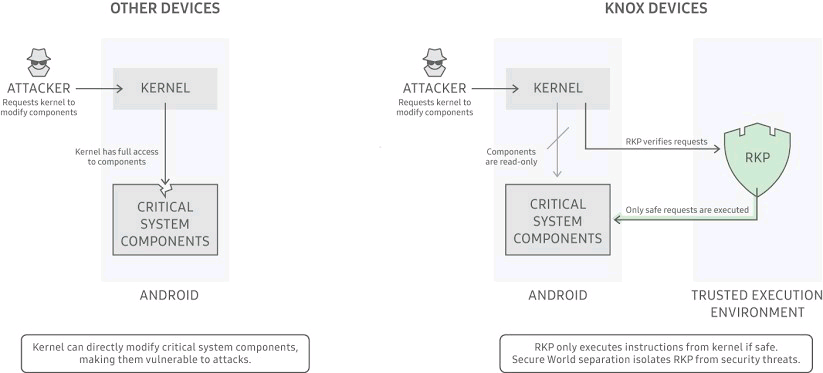
Why does kernel protection matter ??
Kernel protection is central to device security and enterprise data protection.
A compromised kernel can leak sensitive data and even allow remote monitoring and control of the affected device. Other more commonplace protections like Secure Boot or hardware-backed key stores are of little value if the kernel itself is compromised at runtime. After a device boots and decrypts sensitive content, a kernel compromise can result in data leaks that directly impact an enterprise’s data integrity.
Full security coverage
Every year, Samsung’s research and development teams add the latest runtime protections to a growing list of unique capabilities found only within RKP.
Samsung Knox Security solution